Bandit Level 15
-
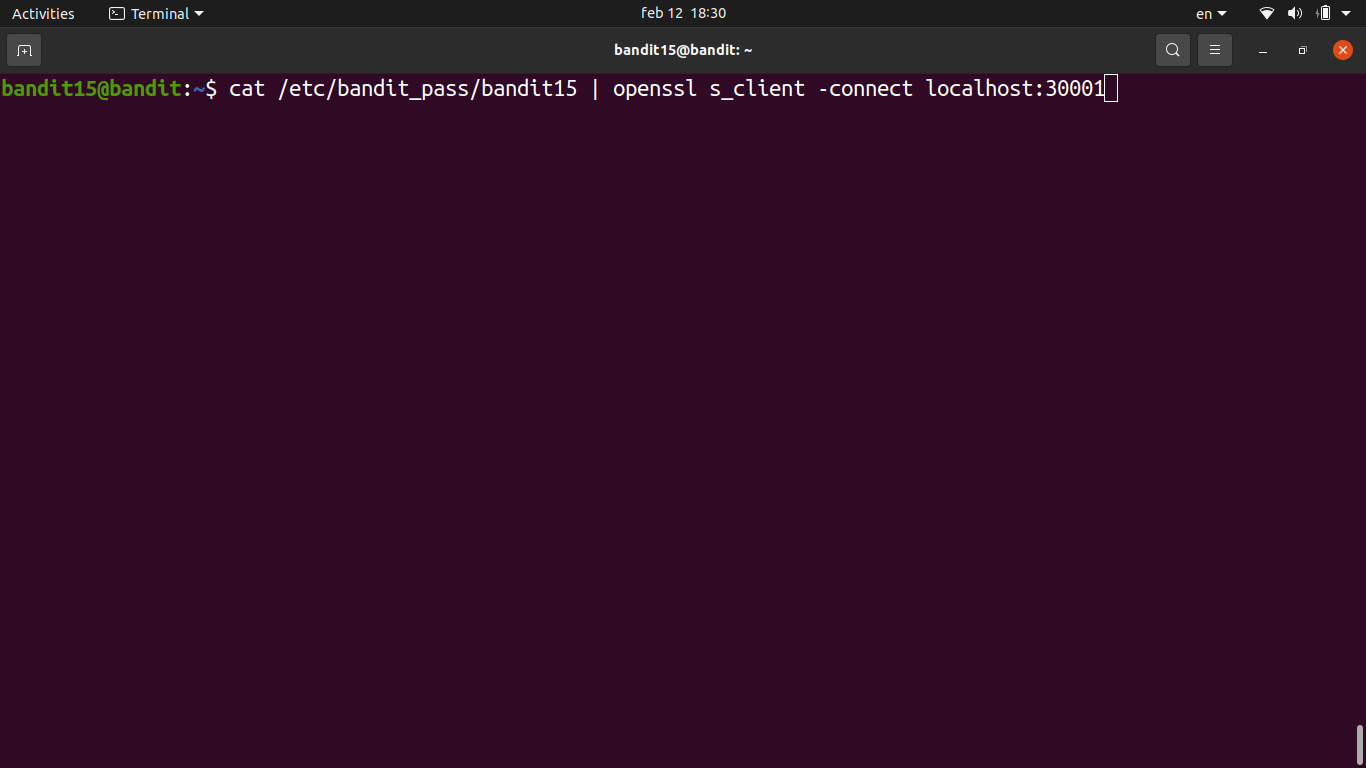
The goal here is to submit the current level’s password to port 30001 on localhost, but this time the connection must be made using SSL/TLS encryption (
ncwon’t work). -
For SSL connections we use
openssl s_client, which is the standard tool for connecting to SSL/TLS-enabled services from the command line.- The
-connectflag specifies the host and port inhost:portformat. - The
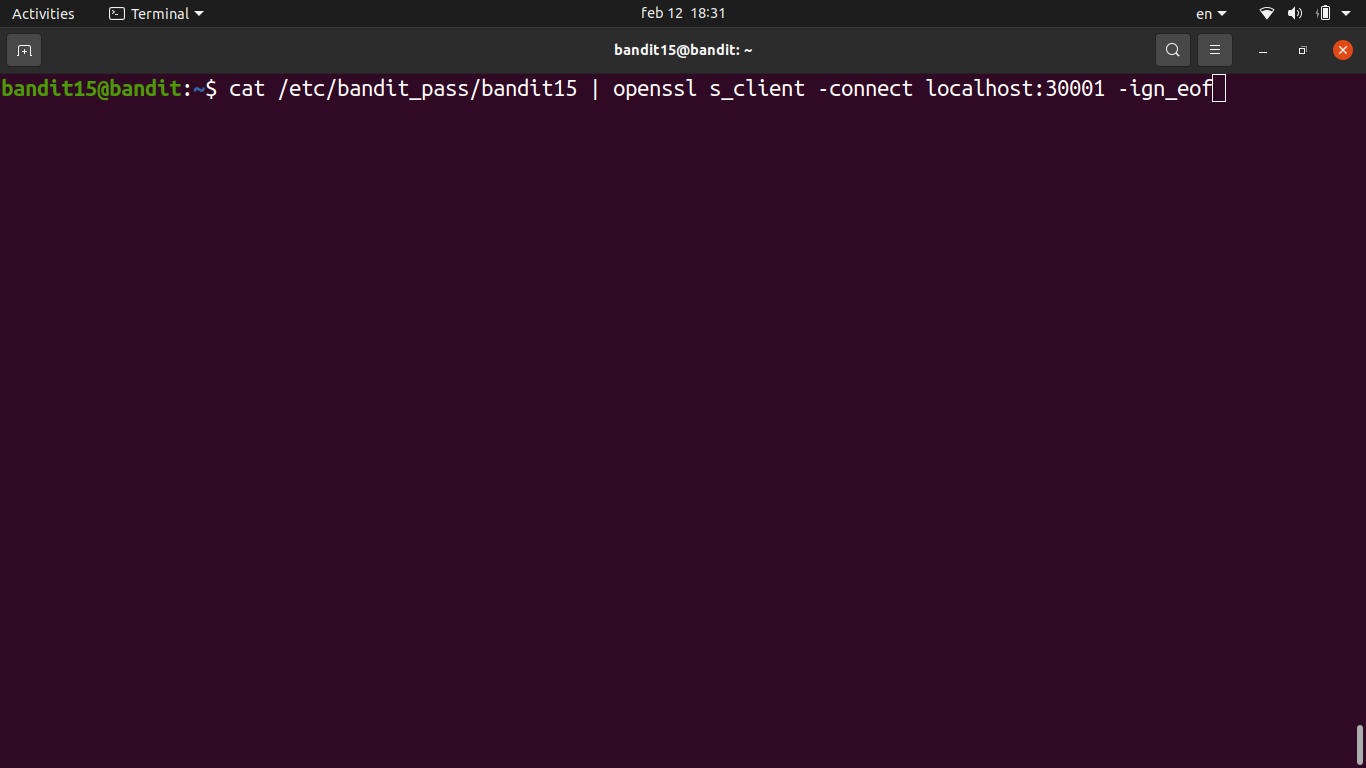
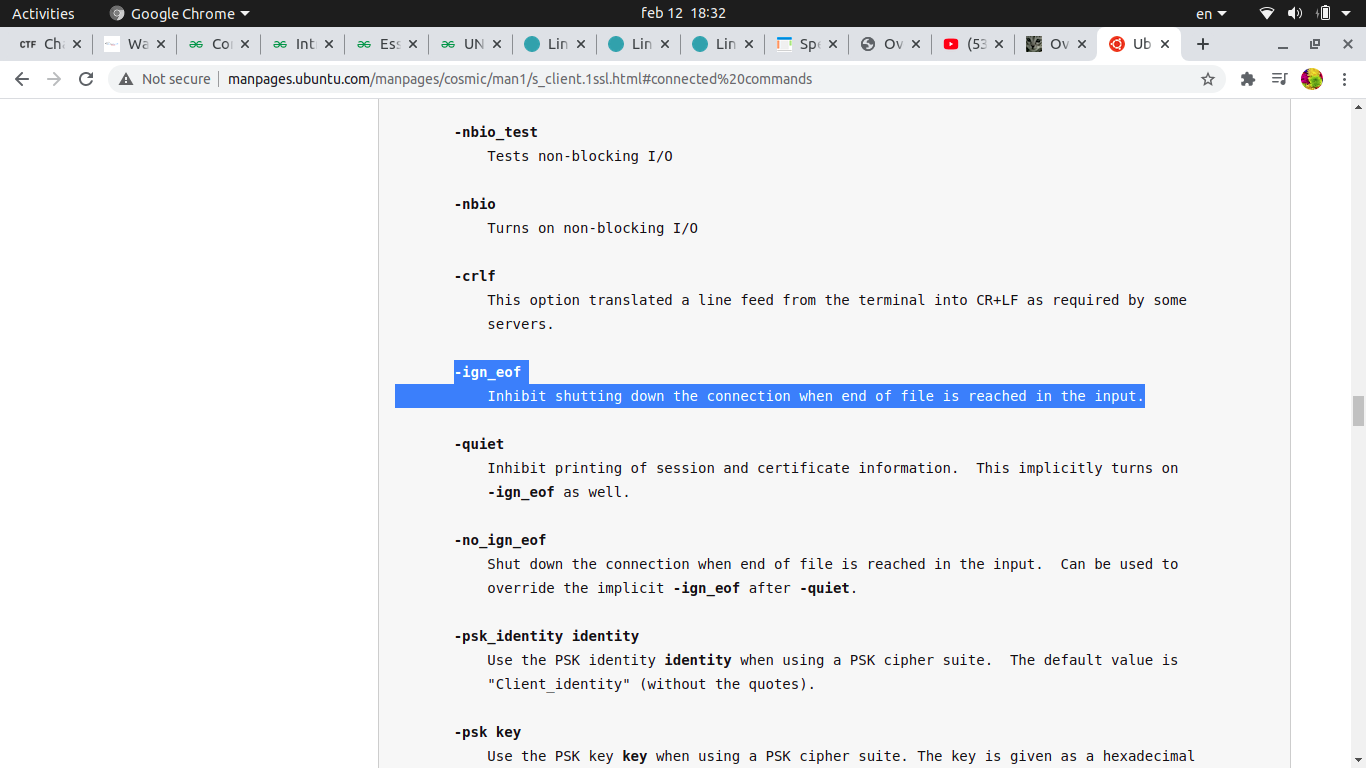
-ign_eofflag tells openssl not to close the connection when it hits EOF, giving us time to type/paste the password.
- The
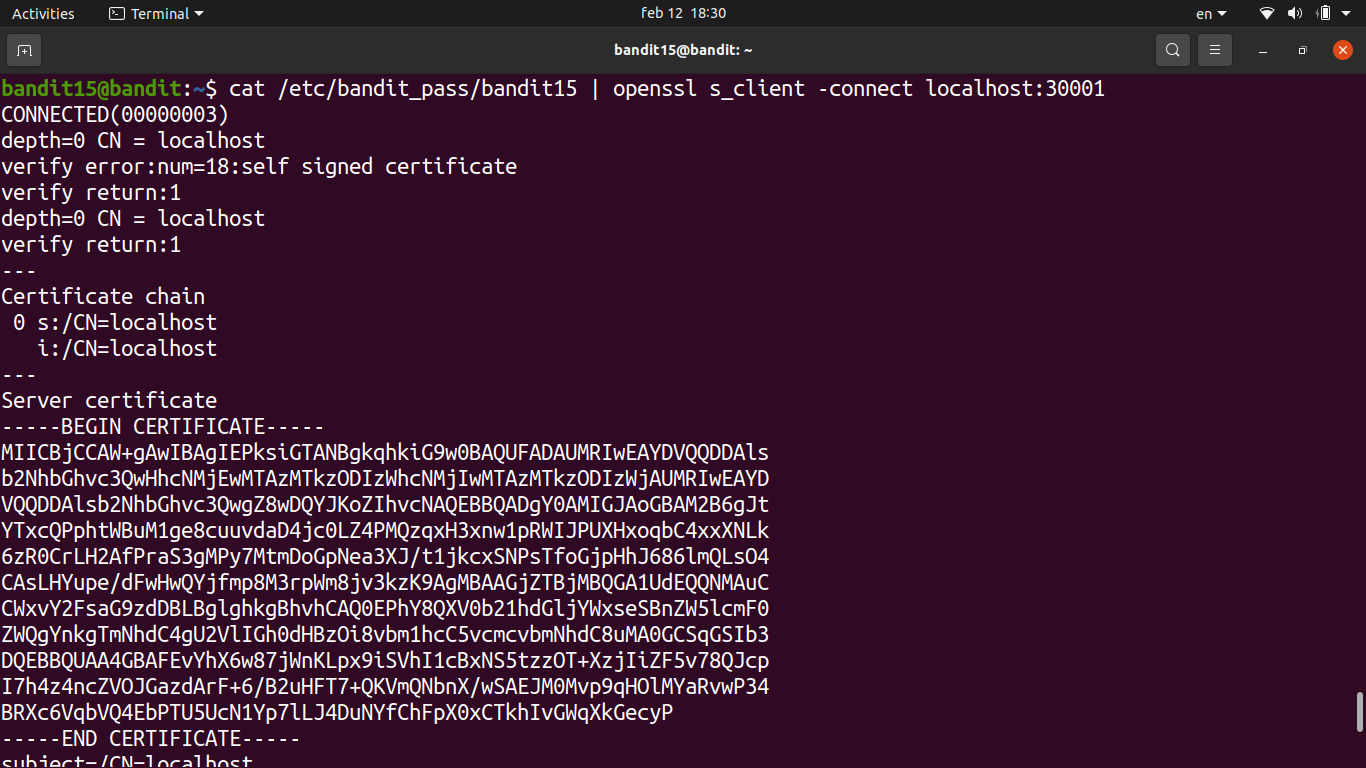
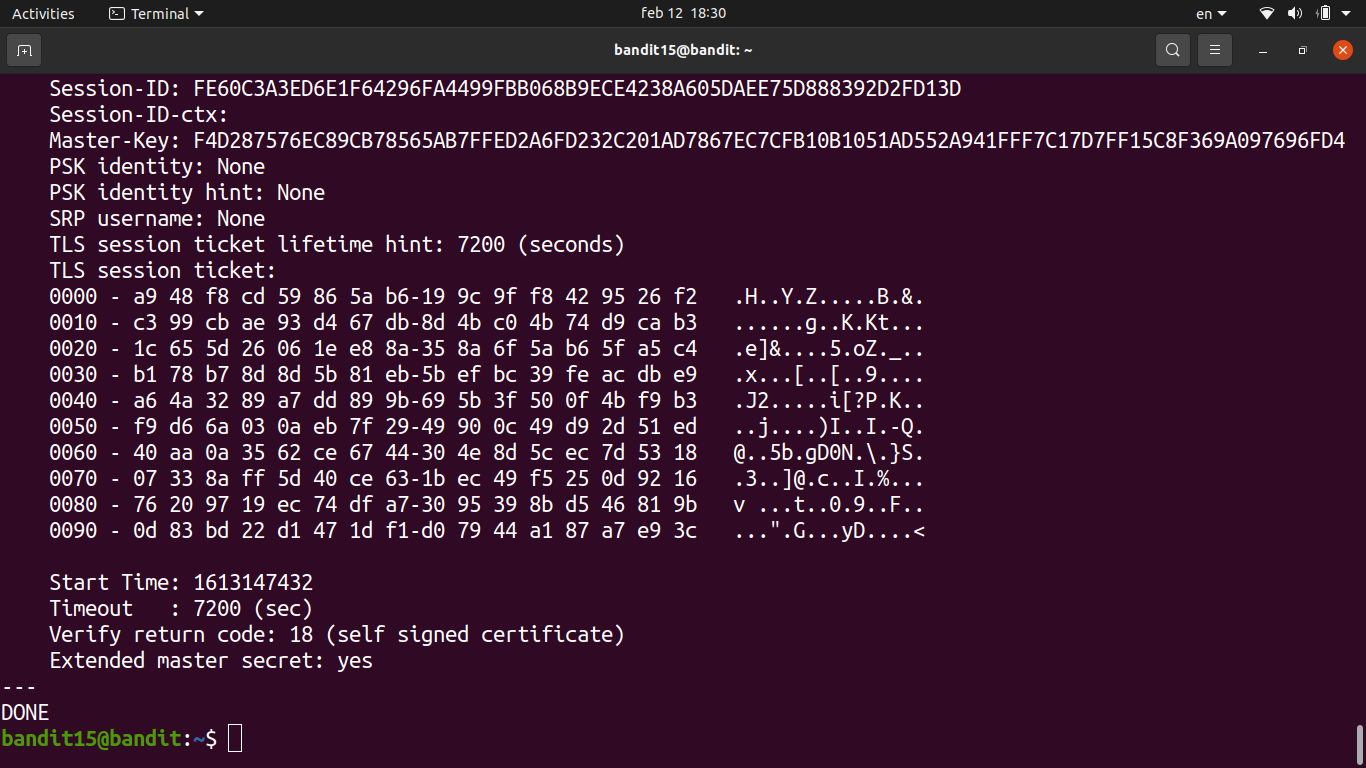
- Connected to the local service on port 30001 via SSL.
- Pasted the current level’s password. The service responded with
Correct!and returned the next password.
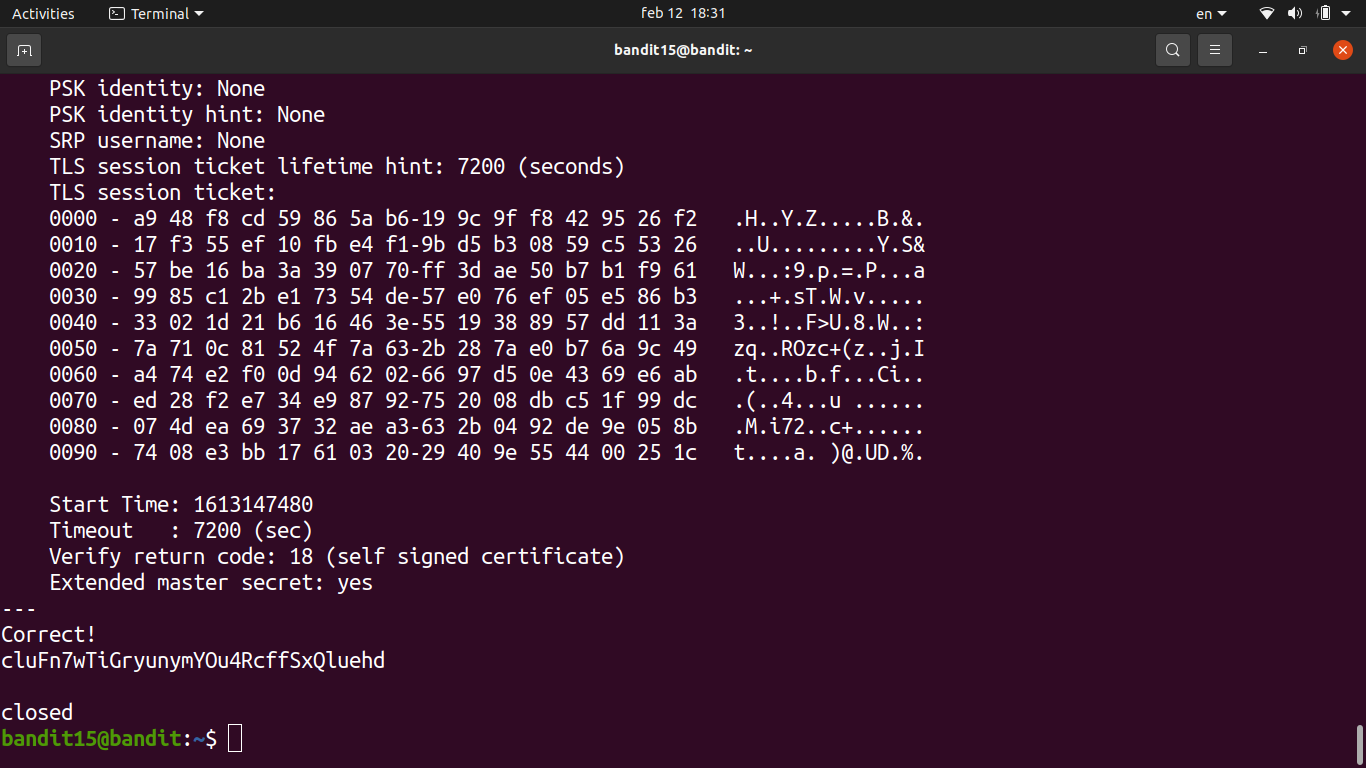
Password
BfMYroe26WYalil77FoDi9qh59eK5xNr