Pentesting Fundamentals
Penetration Testing Ethics
-
Companies that provide penetration testing services are held against legal frameworks and industry accreditation.
-
For example, the National Cyber Security Centre (NCSC) has the CHECK accreditation scheme in the UK.
-
This check means that only “[CHECK] approved companies can conduct authorised penetration tests of public sector and CNI systems and networks.” (NCSC).
-
-
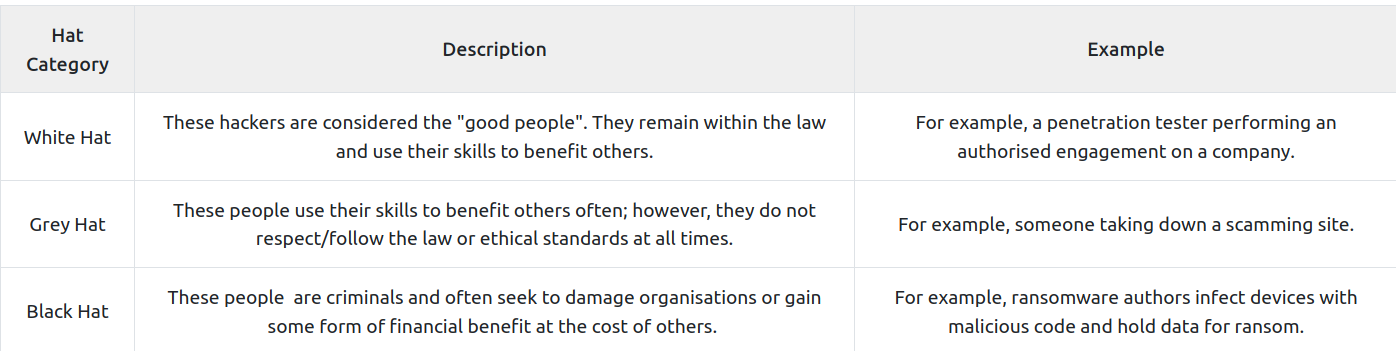
Types of hackers:
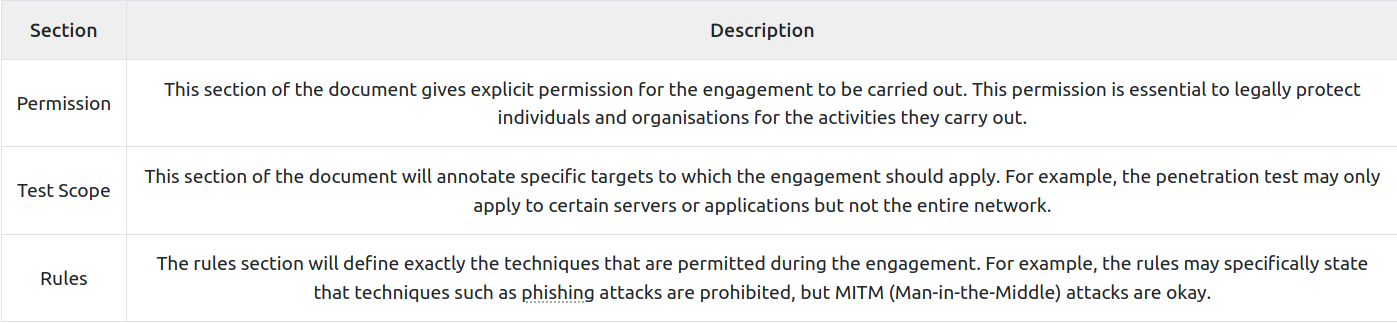
Rules of Engagement (ROE)
- The ROE is a document that is created at the initial stages of a penetration testing engagement.
- This document consists of three main sections (explained in the table below), which are ultimately responsible for deciding how the engagement is carried out.
Questions
- You are given permission to perform a security audit on an organisation; what type of hacker would you be?
R: White hat
- You attack an organisation and steal their data, what type of hacker would you be?
R: Black hat
- What document defines how a penetration testing engagement should be carried out?
R: Rules Of Engagement
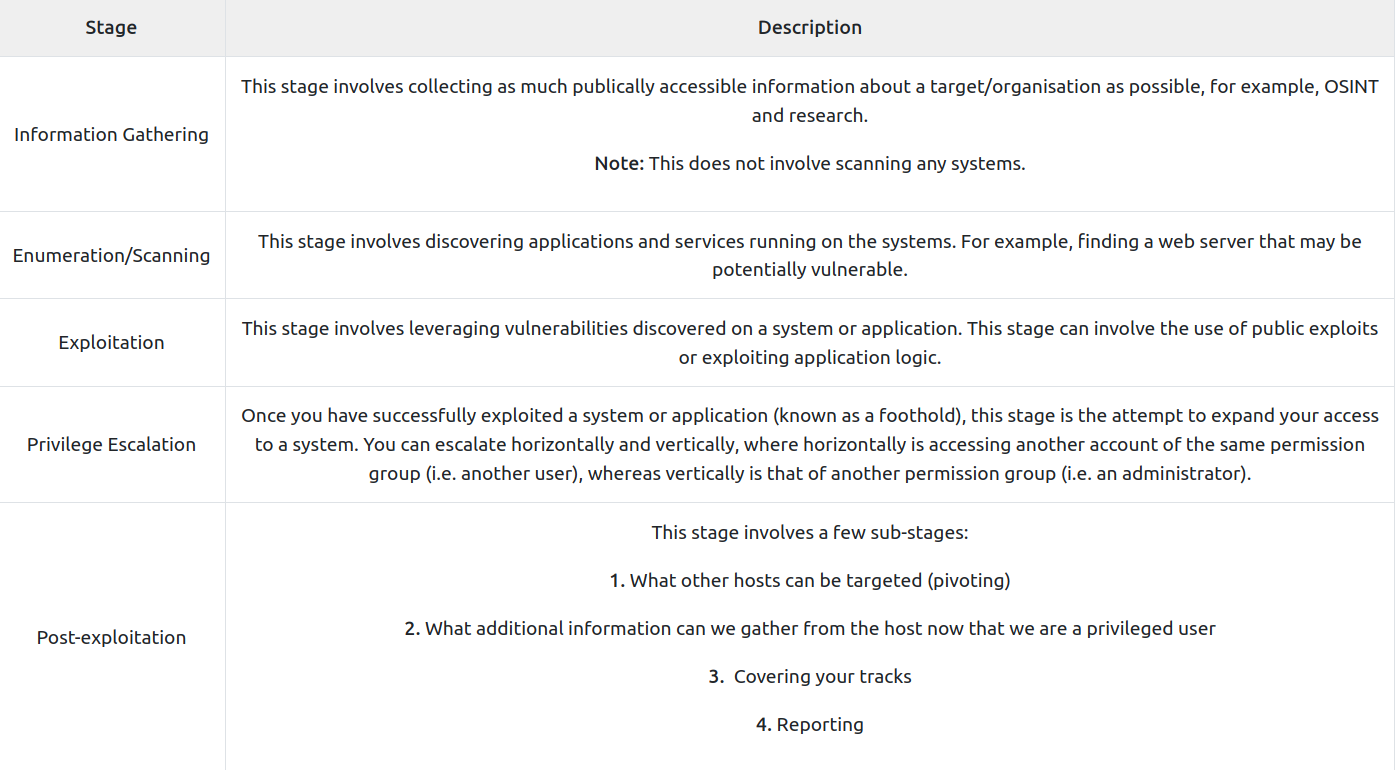
Penetration Testing Methodologies
OSSTMM
- The Open Source Security Testing Methodology Manual provides a detailed framework of testing strategies for systems, software, applications, communications and the human aspect of cybersecurity.
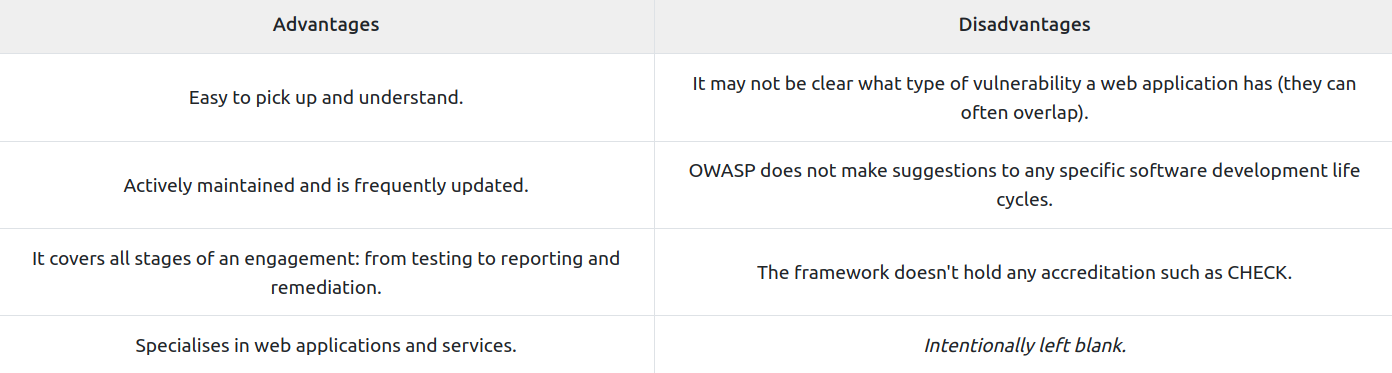
OWASP
-
The “Open Web Application Security Project” framework is a community-driven and frequently updated framework used solely to test the security of web applications and services.
-
The foundation regularly writes reports stating the top ten security vulnerabilities a web application may have, the testing approach, and remediation.
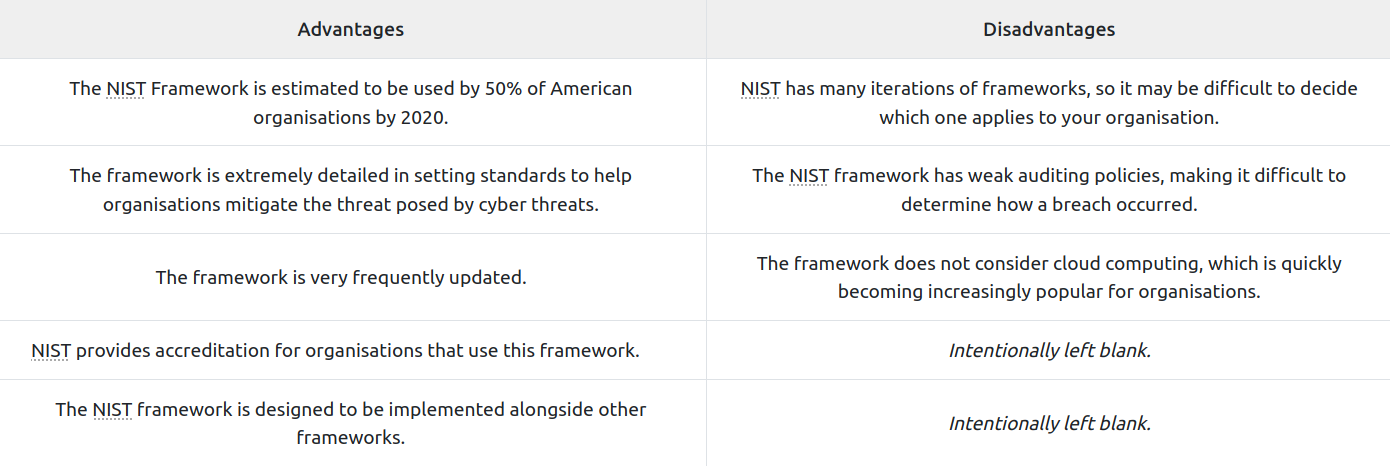
NIST Cybersecurity Framework 1.1
-
The NIST Cybersecurity Framework is a popular framework used to improve an organisations cybersecurity standards and manage the risk of cyber threats. This framework is a bit of an honourable mention because of its popularity and detail.
-
The framework provides guidelines on security controls & benchmarks for success for organisations from critical infrastructure (power plants, etc.) all through to commercial. There is a limited section on a standard guideline for the methodology a penetration tester should take.
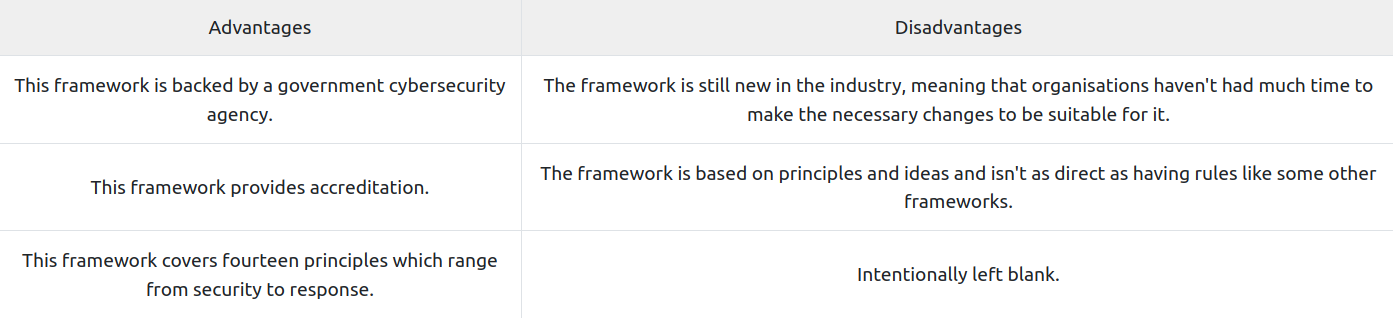
NCSC CAF
-
The Cyber Assessment Framework (CAF) is an extensive framework of fourteen principles used to assess the risk of various cyber threats and an organisation’s defences against these.
-
The framework applies to organisations considered to perform “vitally important services and activities” such as critical infrastructure, banking, and the likes. The framework mainly focuses on and assesses the following topics:
- Data security
- System security
- Identity and access control
- Resiliency
- Monitoring
- Response and recovery planning
Questions
- What stage of penetration testing involves using publicly available information?
R: Information Gathering
- If you wanted to use a framework for pentesting telecommunications, what framework would you use? Note: We’re looking for the acronym here and not the full name.
R: OSSTMM
- What framework focuses on the testing of web applications?
R: OWASP
Black box, WHite box, Grey Box Penetration Testing
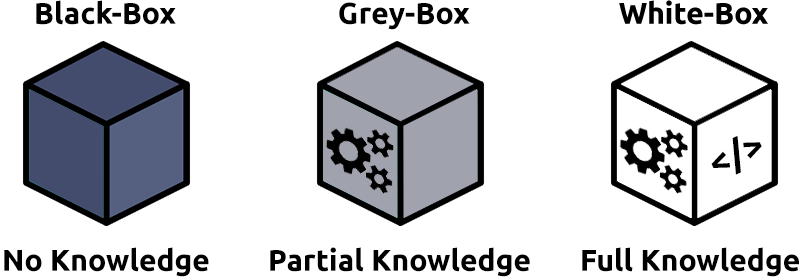
Black Box Testing
-
This testing process is a high-level process where the tester is not given any information about the inner workings of the application or service.
-
The tester acts as a regular user testing the functionality and interaction of the application or piece of software. This testing can involve interacting with the interface, i.e. buttons, and testing to see whether the intended result is returned. No knowledge of programming or understanding of the programme is necessary for this type of testing.
-
Black-Box testing significantly increases the amount of time spent during the information gathering and enumeration phase to understand the attack surface of the target.
Grey Box Testing
-
This testing process is the most popular for things such as penetration testing. It is a combination of both black-box and white-box testing processes. The tester will have some limited knowledge of the internal components of the application or piece of software. Still, it will be interacting with the application as if it were a black-box scenario and then using their knowledge of the application to try and resolve issues as they find them.
-
With Grey-Box testing, the limited knowledge given saves time, and is often chosen for extremely well-hardened attack surfaces.
White Box Testing
-
This testing process is a low-level process usually done by a software developer who knows programming and application logic. The tester will be testing the internal components of the application or piece of software and, for example, ensuring that specific functions work correctly and within a reasonable amount of time.
-
The tester will have full knowledge of the application and its expected behaviour and is much more time consuming than black-box testing. The full knowledge in a White-Box testing scenario provides a testing approach that guarantees the entire attack surface can be validated.
Questions
- You are asked to test an application but are not given access to its source code - what testing process is this?
R: Black Box
- You are asked to test a website, and you are given access to the source code - what testing process is this?
R: White Box
Practical
- Rules of Engagement
Let’s go through the stages of a penetration test assignment for the ACME company.
This stage of the penetration test is where you define three primary objectives. Cycle through the tabs below to explore these.
-
Permission:
- For a penetration test to be ethical and legal, both parties (the company wanting to test their application for vulnerabilities and the company conducting the pentest) will sign a document giving clear permission for the intended actions.
-
Test Scope:
- The test scope will define what targets or environments are being tested against. For example, the client may only want you to test part of their application and not their entire network.
-
Scope:
- The rules define the type of behaviour a penetration tester will employ. For example, you may only have access to part of the application, and not the entire server that hosts it.
- Information Gathering
-
The information gathering stage of an engagement is often undervalued. This stage involves using publicly accessible channels to collect intel on your target.
-
Abbey, who has a public profile on LinkedIn, advertises that she works for ACME and even includes her email in her bio, which is a possible way we can target her work laptop and thus the company.
- Enumeration & Scanning
-
The goal of this stage is to get a complete picture of your target. A penetration tester will try to identify user accounts, machines on their network, network shares, applications etc. Information gathered from stage 2, and the engagement scope document will help in enumerating your target.
-
The enumeration phase is very important as your findings are used to exploit your target’s systems (stage 4).
- Exploitation
-
The exploitation stage involves the knowledge from your enumeration to now identify and exploit vulnerabilities in any of their applications (that are in scope).
-
For example, we enumerated ACME’s website in stage 3 and found that it was vulnerable. We would now exploit this vulnerability, thus (ethically) hacking ACME’s website.
-
Exploitation is the use of a vulnerability discovered to gain un-authorised access to an information security system or data.
- Post Exploitation
-
The post exploitation stage starts when you’ve gained unauthorised access to a system. At this stage of the engagement, your main goals will be to maintain access to the system and escalate your privileges within the system to a super user or administrator user. Systems are usually set up with normal users that don’t have access to various sensitive files and functions - Gaining access to higher privileged users (such as administrators) will allow you to perform actions that you wouldn’t be able to as a normal user (such as reading sensitive files and gaining access to all programs within the system).
-
After doing this, you’ll be extracting sensitive information from the system and attacking other components in the environment (e.g. if the system is part of a network, you will attempt to gain access to other machines in the network).
- Pentest Report & Clearing-up
-
This stage usually occurs at the end of a penetration test. As a penetration tester, you will have to explain the results of your engagement to the client. This is usually done in the form of a report that contains details regarding any security issues you’ve found and how to mitigate them. The client will use this report to understand the security issues and fix the flaws in the technology stack that was tested.
-
It’s also best practice to clean up the environment you’ve been testing (where possible). For example, if you were provided access to machines or tooling by the client, you need to delete any artefacts that have been created as a result of testing.